One of the enterprise’s most valuable assets is its data. People who are committed to being computer hackers often know this. And they use various methods to target companies and access sensitive information about them. The attacks in the network protocols take place in separate layers, for which we need distinct security mechanisms for each type. Different options can secure corporate servers (and even data centers) and secure data from various threats. Let’s discuss two options: Web Application Firewall (WAF) and the Intrusion Prevention System (IPS). This article will focus on the features of WAF vs. IPS.
WAF vs. IPS: Which is better?
To know this, first, let’s discuss WAF and IPS
Web Application Firewall (WAF)
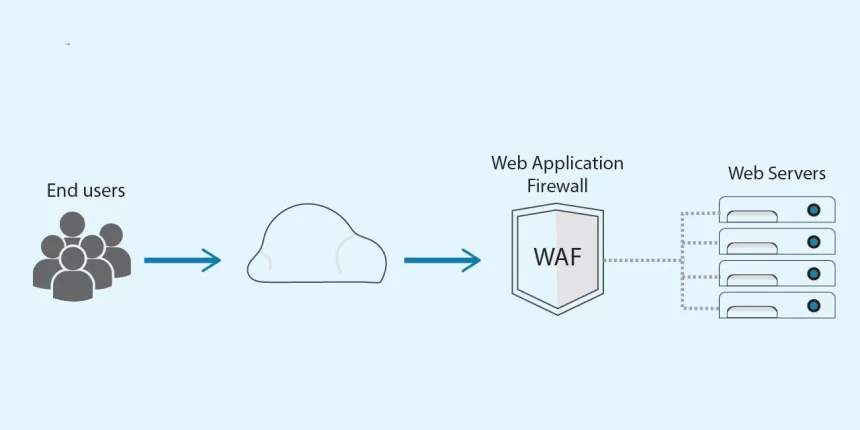
WAF is a solution (software or hardware) that acts as an intermediary between web applications and external users. This ensures that the WAF analyzes all HTTP communication (request-response) before it hits the web apps or users. To track and analyze the HTTP traffic, WAF applies previously defined rules that make it possible to detect malicious HTTP requests. When the WAF senses a threat, it blocks the traffic and rejects the request of sensitive data from the malicious site. If there are no attacks or threats, all the traffic will usually flow. Organizations have robust firewall policies in place to double their defenses. Most of them also utilize a firewall policy analyzer to assess the adequacy of their policies and fine-tune them to address the evolving threats.
Intrusion Prevention System (IPS)
An Intrusion Prevention System (IPS) is a type of network security that works to identify detected threats and prevent them. Intrusion prevention systems track the network continuously, looking for potential malicious events and collecting information on them. The IPS reports these incidents to network administrators and takes proactive measures to prevent possible attacks. IPS tools may also be used to detect issues with corporate security policies. It acts by stopping staff and network visitors from violating the rules found in such policies.
WAF vs. IPS: Key Difference
An IPS is simply based on signatures and is not conscious of sessions and users trying to access a web app. On the other hand, a WAF is aware of meetings, users, and programs that attempt to access a web application. The significant difference between the two technologies is the level of intelligence required to analyze traffic on Layer 7.
Firewalls
WAF (Web Application Firewall) and IPS (Intrusion Prevention System) are often confused with the firewall. A firewall is a network security protocol that controls incoming and outgoing communications (blocks or permits) based on predetermined security rules.
Difference between a Firewall, WAF and IPS
These are all systems that allow network traffic to pass through or be blocked, but generally speaking, the main difference is that each of them protects the different layers.
- Firewall: Determines whether to block or permit the network traffic based on port numbers or IP addresses.
- WAF: Decides whether to allow or block network traffic on the application layer based on the communication content.
- IPS: Monitors OS and network traffic to prevent unauthorized communications and changes.
Conclusion
In conclusion, WAF is useful for protecting HTTP applications and is typically used to secure servers. It is aware of such web traffic as HTTP GET, POST, URL, SSL, etc. On the other hand, IPS provides protection for a wide range of network protocols and can perform raw protocol decoding and detect abnormal behavior. IPS is not aware of sessions (GET/POST), users, or even applications.
It is clear that even the two solutions provide an extra layer of security for our network; they operate on specific traffic types. And they often complement each other rather than compete. Although IPS appears to protect broader traffic, there is a very particular one with which only a WAF can work. So it is recommended to have both solutions, mainly if the web works close