Modern security technologies help to protect companies’ assets. But they can also help to boost business efficiency.
Let’s take a look at some innovations that enhance both security and efficiency – so you can choose the right solutions for your business needs.
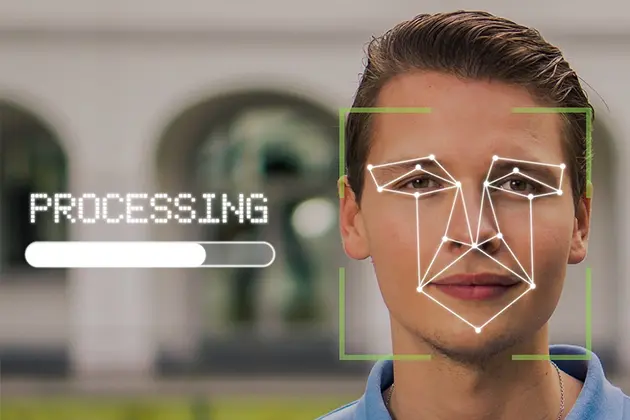
Enhancing Physical Security with Smart Surveillance Systems
Security cameras today do more than just record. Modern systems include AI-powered features like facial recognition, motion tracking, and behavioral analysis. These tools identify threats quickly and accurately, helping businesses respond before problems escalate.
Imagine a store owner receiving a mobile alert about unusual after-hours activity caught on camera. They can act immediately (such as calling security or the authorities) – and thus save time and protect assets effectively.
Smart surveillance also supports business efficiency by streamlining monitoring processes through automation. Instead of constant manual oversight, owners receive targeted updates based on actual risks or events detected by the system itself.
This combination of enhanced protection and reduced effort makes these technologies an invaluable part of physical security planning.
Integrated Alarm Systems for Immediate Threat Response
Alarm systems have come a long way from basic noise-makers. Modern options integrate with other security measures, like surveillance cameras and access controls, to offer faster responses and better coverage.
Think about how quickly a fire or intrusion can escalate without immediate action. An advanced alarm system not only detects these threats but also automatically notifies key personnel or emergency services in real time. This rapid response minimizes damage and downtime.
Some systems even use analytics to predict potential risks by monitoring patterns (like repeated failed access attempts) to flag vulnerabilities before incidents occur.
By combining quick alerts with preventive insights, integrated alarms keep businesses efficient while safeguarding assets around the clock.
The Role of Commercial Door Operators in Business Safety
Doors aren’t just entryways – they’re critical to a business’s security and efficiency.
During peak warehouse hours, for example, automated doors improve workflow by enabling swift access without compromising safety.
Many companies rely on reliable door operators for businesses because they reduce downtime and unauthorized access simultaneously.
Also, their precision design prevents wear and tear over time, which helps lower maintenance costs.
With customizable features to fit operational needs, commercial door operators enhance both protection and efficiency while keeping daily processes running smoothly.
Reducing Theft Risks with Inventory Monitoring Technologies
Inventory theft, whether internal or external, can hurt a business’s bottom line. Advanced monitoring systems now make it easier to track stock and reduce risks.
These systems often use RFID tags or barcode scanners connected to centralized software.
They provide real-time updates on inventory movement, ensuring accuracy and highlighting unusual activity immediately. For example, if an item leaves a storage area without authorization, the system sends alerts for quick action.
Such tools also improve efficiency by eliminating manual counting errors and streamlining audits.
With better oversight and quicker responses in place, businesses can safeguard their assets while maintaining smoother operations across their supply chains.
Fire and Environmental Sensors: Preventing Damage Before It Starts
Environmental threats like fires or water leaks can devastate businesses if not detected early. Modern fire and environmental sensors act as vigilant sentinels, continuously monitoring conditions to catch problems before they escalate.
Imagine a small warehouse where a leak starts unnoticed. Without detection, it damages inventory and infrastructure over time. But with sensors in place, an alert notifies management immediately, allowing swift action to prevent costly damage.
These systems also integrate with alarms or automated shut-off valves for an instant response when thresholds are breached.
By mitigating risks quickly, fire and environmental sensors protect assets while minimizing downtime – a practical approach that ensures business continuity no matter the circumstances.
Protecting Digital Assets with Cybersecurity Measures
In today’s digital landscape, safeguarding data is just as critical as securing physical assets. Businesses face growing threats from cyberattacks, making advanced cybersecurity measures essential.
Tools like firewalls, multi-factor authentication (MFA), and endpoint protection software provide layers of defense against breaches. For example, MFA requires users to verify their identity twice (like a password and a phone code) – thus reducing unauthorized access risks significantly.
Beyond tools, automated monitoring systems detect unusual network activity in real time and send alerts before serious damage occurs. This proactive approach not only protects sensitive information but also prevents operational disruptions caused by downtime or stolen data.
Remember: secure digital practices directly impact business efficiency and reputation alike.