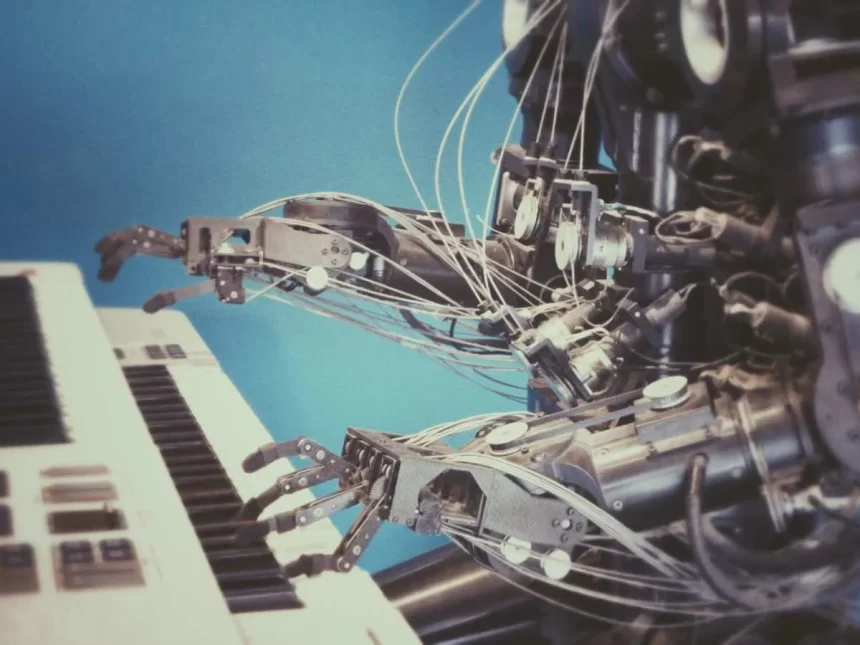
As the IT industry has been disrupted by the new-age technology, several trend issues frequently attract attention. Automating mundane and repetitive tasks has become a vital dose for progressive companies. It frees the workers from this mission and leads them to more innovative work. From a cyber-security perspective, the focus may be more on innovation and leadership quality. As automation can solve Cybersecurity problems with itself, cybersecurity programs should be ready for automated solutions at the forefront, giving rise to another innovative Cybersecurity Automation approach.
Analyzing Cybersecurity Automation
The new automation practices generally refer to tools such as SOAR (Security Automation and Orchestration) products, RPA, and custom-developed software code. These automate the process and conduct the analysis. SOAR products are purpose-built tools that act as instruments between other tools of protection. It also carries out specific automation activities to discover risks. RPA tools are a more comprehensive set of automation tools that automate a wide variety of processes. These methods are being implemented rapidly in the HR and Finance fields. Cybersecurity teams should use it too. Custom-developed software and code can automate all sorts of analyzes. It is often leveraged for a niche or other obstacle inside a company lacking the availability of an out of the box tool. All three approaches interact with an enterprise’s orchestration to gather intelligence, perform analyzes and take-automated action, or prompt a team member to take additional action.
Need for Cybersecurity Automation
If cybersecurity cannot adequately manage the changing ecosystem, the new-found affection for digital transformation can lead to increased organizational complexity leading to certain risks. Several companies manually inspect systems and data to gather evidence of unforeseen behavior and detect compromising or defect indicators. Cybersecurity automation can address such a losing proposition in new-age firms. It can support and fix poorly proportioned cybersecurity teams as well. Since it is quite unrealistic to expect humans to catch potential cybersecurity events reliably, leveraging automation could be significant to safeguard the organization reliably.
Perks of Cybersecurity Automation
Through its implementation, an organization’s cybersecurity team can focus on more complex activities that imply machines can perform repetitive tasks. Cybersecurity teams can dedicate themselves to more critically creative technical work to address issues and organizational risk posture. This will allow the cybersecurity team to focus on the development and implementation of cybersecurity strategies. The shortcomings found from some automation efforts will benefit the technical and task teams while providing the company with more routine and actionable insight. Automation will become a vital component of the cybersecurity program that would need its resources related to the ongoing and iterative design and implementation of automation.
Basic Ways of Implementing Automation Principles Effectively
The cybersecurity team should be integrated with development capabilities that allow developers to report to cyber leadership directly. Cybersecurity partnership with organizational development teams will enable cybersecurity to enforce the capabilities of such teams’ experts. Adopt a hybrid strategy that will use an internal team for complex integration research for operational development work and organizational growth capabilities. The need for safety automation tools and techniques will continue to grow with the continuous increase in cybersecurity complexity. It will soon become an integral part of an organization’s perspective roadmap on cybersecurity.
The Future of Cybersecurity Automation
Until now, it can be seen that the future of cybersecurity is tightly interwoven with automation. Some teams are likelier to become smarter in terms of codes and development practices in the future of cybersecurity. It can be expected that the cybersecurity system can become a developer shop that will foster automation capabilities that are generated and advanced across multiple techniques.